The cyberthreat landscape has transformed significantly with identity-based attacks emerging as a dominant threat vector. The 2025 Identity Threat Research Report, “Identity-Centric Threats: The New Reality,” presents findings from research conducted by the eSentire Threat Response Unit (TRU) on shifting tactics, how they bypass traditional cybersecurity controls, and implications on organizational security posture. Download your complimentary copy of the report.
Monthly Archives: October 2025
Embarking on the Microsoft Teams Premium Adoption Journey
Microsoft Teams Premium is the solution many organizations use to help employees benefit from seamless collaboration and security. Look at this thought-provoking blog showing the four-stage process of rolling out Teams Premium to ensure that your workforce adopts its features and advantages.
Identity-Centric Threats: The New Reality
The cyberthreat landscape has transformed significantly with identity-based attacks emerging as a dominant threat vector. The 2025 Identity Threat Research Report, “Identity-Centric Threats: The New Reality,” presents findings from research conducted by the eSentire Threat Response Unit (TRU) on shifting tactics, how they bypass traditional cybersecurity controls, and implications on organizational security posture. Download your complimentary copy of the report.
Managed Detection and Response
As cyber threats grow increasingly sophisticated, businesses need more than just technology — they need experts who can detect and respond to threats in real-time. The eSentire Difference lies in its human-led, AI-supported approach, offering rapid detection and response to emerging threats. Download the datasheet to see why eSentire is trusted for comprehensive MDR and connect with Mowry International to discuss implementing this solution.
Identity-Centric Threats: The New Reality
The cyberthreat landscape has transformed significantly with identity-based attacks emerging as a dominant threat vector. The 2025 Identity Threat Research Report, “Identity-Centric Threats: The New Reality,” presents findings from research conducted by the eSentire Threat Response Unit (TRU) on shifting tactics, how they bypass traditional cybersecurity controls, and implications on organizational security posture. Download your complimentary copy of the report.
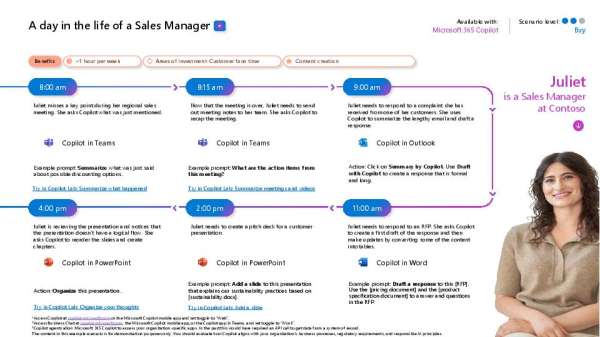
Navigating a Sales Managers Day with Copilot
Sales managers face a constant balancing act. From leading teams, managing customer interactions, and driving revenue, it can all be overwhelming. This infographic illustrates a full day in the life of a sales manager using Microsoft Copilot, with clear examples of how AI simplifies core processes. Check it out to see where Copilot can save time and boost productivity. Contact Mowry International to discuss how to take advantage of Copilot’s offerings.
🔒 Is your security strategy strong enough? DM us for a security assessment and build a Zero Trust foundation with Microsoft Security. @msftsecurity #ZeroTrust
Identity-Centric Threats: The New Reality
The cyberthreat landscape has transformed significantly with identity-based attacks emerging as a dominant threat vector. The 2025 Identity Threat Research Report, “Identity-Centric Threats: The New Reality,” presents findings from research conducted by the eSentire Threat Response Unit (TRU) on shifting tactics, how they bypass traditional cybersecurity controls, and implications on organizational security posture. Download your complimentary copy of the report.
Sizes for Virtual Machines in Azure
Microsoft Azure provides a wide range of sizes and types of virtual machines to address your organization’s needs. These specialized virtual machines are available with single, multiple, or fractional GPUs. These sizes are designed for compute-intensive, graphics-intensive, and visualization workloads. This interactive table provides you with a quick and easy description of each type. Explore what Microsoft Azure has to offer! Contact us for a personalized demo.
Randomized controlled trial for Microsoft Security Copilot
This white paper shares results from a rigorous, randomized controlled trial of Microsoft Security Copilot. Download the whitepaper to see the results and learn how Copilot can elevate your SOC’s performance. Connect with Mowry International for a strategic security consultation.
View: Randomized controlled trial for Microsoft Security Copilot